/fit-in/1440x9999999/prod01/channel_3/media/images/banner-left-block-3000X1200/Cybersecurity-AdobeStock_87909563_3000X1200.png)
Cyber Security
Imperial College London is recognised as one of the UK's leading universities in cyber security research
Imperial College London’s cyber security research focuses on the engineering and design of secure and resilient systems, led by academics across the Departments of Computing, Mathematics, and Electronic and Electrical Engineering.
Imperial has been recognised as an Academic Centre of Excellence in Cyber Security Research (ACE-CSR) by the National Cyber Security Centre (NCSC) continuously since the inception of the scheme in 2012.
Research themes
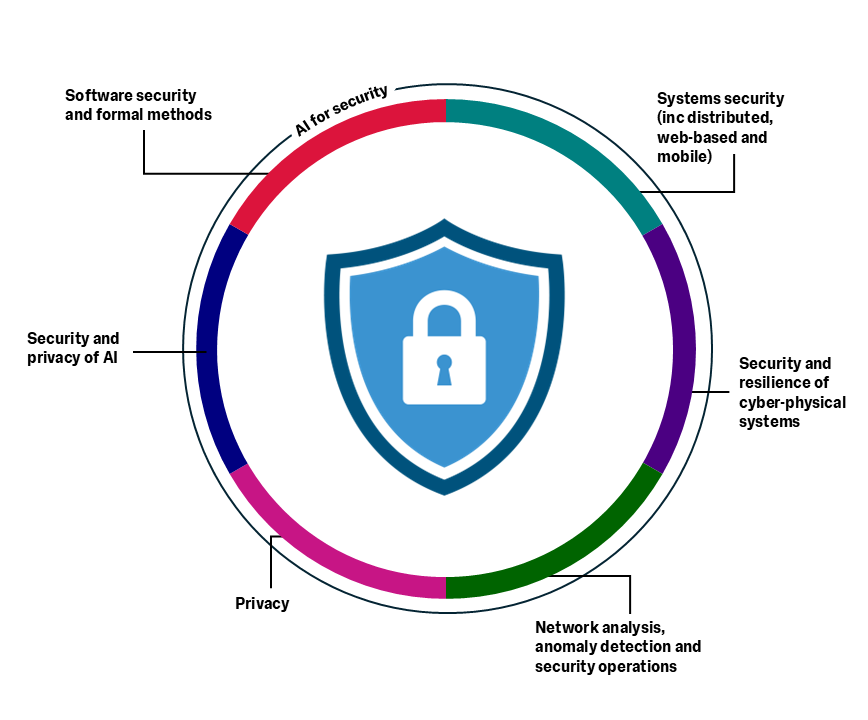
We broadly categorise our research activities as follows:
- Software security and the use of formal methods
- Systems security
- Security and resilience of cyber-physical systems
- Network analysis, anomaly detection and security operations
- Privacy
- Security and privacy of AI
Find a full list of our cyber security related publications
Find out more about cyber security at Imperial and browse the following links:
Find out more
menu
News
More news10 December 2020
Imperial cyber security expert announced as GCHQ Fellow

